Every product in your supply chain passes through warehouses, docks, shipping hubs, and retail channels before reaching the customer. Along the way, every handoff creates a security risk. Inventory security is critical as theft, tampering, and inventory discrepancies can happen faster than most businesses expect.
That’s why inventory security has become a business priority. If you want to protect profits and maintain customer confidence, you need systems that secure inventory from the warehouse floor to the final delivery. Here’s how businesses are reducing risk across the supply chain.
Why Inventory Loss Keeps Growing
Inventory loss no longer comes only from shoplifting or warehouse theft. Today, supply chains face organized cargo crime, internal fraud, cyber manipulation, and shipping errors. Criminal groups target high-value products during transit because they know logistics networks rely on multiple third-party partners.
Internal mistakes also create losses. Poor scanning practices, delayed reporting, and inaccurate stock counts weaken inventory control. If employees can bypass procedures or override records without oversight, discrepancies become harder to detect.
When inventory disappears or arrives compromised, customer trust drops quickly. Returns increase, and your reputation can take a direct hit.
Building Visibility Across the Supply Chain
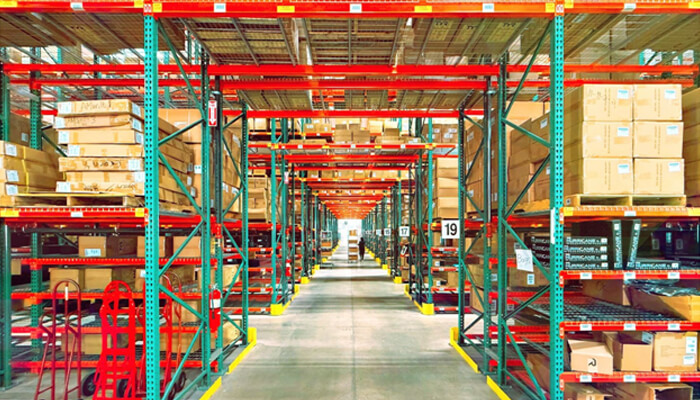
Strong inventory security starts with visibility. You can’t protect what you can’t track. Modern businesses rely on real-time monitoring systems to follow inventory from receiving to delivery. Barcode scanning, RFID tags, and cloud-based inventory software help identify gaps before they become expensive problems.
Real-time tracking also improves accountability. Every movement gets logged, time-stamped, and tied to a specific user or location. That creates a clear chain of custody across operations. If inventory goes missing, you can investigate faster and isolate the source of the issue.
Data analytics adds another layer of protection. Modern platforms can detect unusual movement patterns, repeated adjustments, or suspicious shipping activity. Instead of waiting for monthly audits, you can respond to risks immediately.
Strengthening Warehouse Access Control
Warehouse security depends heavily on controlled access. Too many facilities still rely on outdated methods like shared keys or open loading zones. Stronger access control reduces those risks significantly.
You should limit entry based on employee roles and responsibilities. Keycard systems, biometric access, and digital logs help monitor who enters sensitive areas and when. Restricted access zones work especially well for high-value products and confidential materials.
Surveillance systems also play an important role. Modern security cameras powered by AI can identify unusual activity, monitor blind spots, and support investigations. Consistent monitoring often improves compliance with security procedures.
Preventing Tampering During Storage and Transport
Product tampering creates serious financial, legal, and safety risks, especially for food, pharmaceuticals, electronics, and luxury goods. To reduce exposure, businesses often combine two or more of the following strategies:
- Secure packaging: Reinforced cartons, shrink‑wrap, and sealed containers make products harder to tamper with in storage or transit. Breaches leave clear signs, discouraging interference and helping businesses spot compromised goods quickly.
- Controlled loading: Structured loading procedures and chain‑of‑custody checks block unauthorized substitutions. Each handoff is logged and confirmed, closing common tampering gaps during transfers.
- Security seals: When applied to containers, pallets, and shipping cases, security seals provide clear evidence of tampering and highlight unauthorized access. They deter interference and create a traceable record for faster investigation.
- Environmental monitoring: Sensors, GPS, and smart devices flag route changes or condition shifts that suggest tampering. Real‑time alerts let managers intervene before compromised shipments move further.
Layering these measures helps companies respond quickly to risks and maintain product integrity throughout storage and transit.
Using Automation to Reduce Human Error
Human error remains one of the biggest inventory security challenges. Employees may scan products incorrectly, misplace shipments, or skip verification steps under pressure. Automation helps reduce those risks while improving consistency.
Automated inventory systems minimize manual data entry and reduce opportunities for manipulation. Robotics and automated storage systems also improve accuracy in fulfillment centers. When processes become standardized, inventory handling becomes more predictable and secure.
Artificial intelligence now helps businesses forecast risk patterns as well. AI tools can flag suspicious purchasing behavior, detect irregular shipping activity, and identify anomalies in inventory movement.
Leveraging Third‑Party Security Partnerships
Even the strongest internal systems can’t protect inventory alone. Modern supply chains rely on carriers, suppliers, and external warehouses, and each handoff can become a weak link if standards aren’t aligned. Building resilience means extending your security culture beyond company walls and into every partner relationship.
Shared protocols, verified compliance, and collaborative monitoring help close those gaps. When partners follow the same procedures, audits confirm adherence, and data feeds integrate into your visibility platforms, you maintain a unified chain of custody. Treating external partners as extensions of your own security culture reduces blind spots and strengthens protection across the entire supply chain.
Creating a Security Culture That Lasts
Technology alone won’t solve inventory security problems. A lasting solution requires a culture built around accountability, communication, and consistency. Core practices include:
- Employee training and education: Employees should learn inventory protocols, reporting procedures, and security expectations from the start. Ongoing training reduces accidental losses and makes suspicious behavior easier to recognize.
- Encouraging reporting: Create an environment where employees feel confident reporting suspicious activity quickly.
- Consistent reinforcement: Managers must apply procedures consistently, even during busy periods, to prevent rules from being treated as optional.
Regular audits provide the check‑ins that confirm procedures are working and highlight where improvements are needed. With everyday practices supported by periodic review, security becomes a living part of operations rather than a static rulebook.
Conclusion
Modern supply chains move faster than ever, but speed without security creates costly vulnerabilities. Inventory loss, tampering, and operational disruptions can damage profits and customer trust. Businesses that invest in visibility, automation, access control, and tamper prevention build stronger operations from the ground up.
When you treat inventory security as a long-term strategy instead of a short-term fix, you create a supply chain that performs with greater accuracy and resilience. Most importantly, you gain the ability to protect your products at every stage of the journey.