If you are searching for how HCS 411GITS software built, you have probably noticed something confusing — there is no clear official explanation of how this software is actually developed. Different sources describe it in different ways, and many articles make confident claims without strong evidence. This guide breaks down what can realistically be trusted, what is inferred, and how software like HCS 411GITS is actually built in practice.
Many articles on this topic sound more certain than the evidence actually allows. That is a problem. When people search how HCS 411GITS software built, they usually want a reliable explanation of the software’s architecture, workflow, and development process, not a stack of guesses presented as fact.
Who Should Read This Article
- Developers trying to understand system architecture
- IT professionals evaluating workflow software
- Students learning how complex software is built
- Business owners exploring enterprise platforms
What Can Be Said Publicly About HCS 411GITS
Confirmed vs Inferred Information
The table below highlights what is publicly known and what should be treated as inference when analyzing this software.
| Topic | Publicly described | Confirmed publicly? | Best way to present it |
|---|---|---|---|
| Workflow-heavy software | Yes | Partly | Say “appears to be” |
| Modular architecture | Implied | No | Present as likely inference |
| Exact tech stack | Mentioned in discussions | No | Do not state as fact |
| Cloud or hybrid hosting | Claimed by some sources | No | Treat as unverified |
| API integrations | Mentioned in update-style sources | Partly | Present cautiously |
| Security controls | Not clearly documented | No | Explain as standard practice |
What HCS 411GITS Is Likely Used For
How HCS 411GITS Software Built in Practice
The best way to answer how HCS 411GITS software built is to combine the limited public descriptions with established software engineering practice.
1. Requirements and planning
A system described as workflow-heavy or operational would normally start with requirements gathering, stakeholder input, workflow mapping, and risk identification. NIST’s Secure Software Development Framework is built around integrating secure practices into each implementation of the software development lifecycle, and OWASP’s developer guidance also treats requirements, design, implementation, and verification as connected parts of secure development.
That means a realistic starting point for HCS 411GITS would include defining:
- What processes must the software support
- Which users need access
- What data does the system store or move
- Which external systems must it connect to
- What security, reliability, or compliance constraints apply
This is not product-specific proof. It is the most credible explanation of How HCS 411GITS Software Built in systems of similar complexity.
2. Modular architecture
The public descriptions suggest multiple responsibilities rather than a tiny, narrow tool. ScoopMeadow explicitly talks about microservices, edge-cloud computing, and real-time processing, though those claims come from a secondary site and should not be treated as officially verified product documentation. Even if those details are uncertain, the broader idea of modular architecture still fits the way HCS 411GITS is described across sources.
A likely architecture for software of this type would include:
| Layer | Likely purpose |
| Frontend | Dashboards, forms, controls, reports |
| Backend | Business rules, workflow logic, and processing |
| Database | Records, logs, configuration, and historical data |
| Integration layer | APIs, connectors, system-to-system exchange |
| Security layer | Authentication, authorization, validation, auditability |
| Monitoring layer | Logs, alerts, health checks, performance visibility |
This table is an inference based on system behaviour, not a confirmed internal diagram. It reflects a realistic view of How HCS 411GITS Software Built based on common architectural patterns.
3. Collaborative development with version control
Git’s documentation explains branching as a way to diverge from the main development line without affecting it, which is a standard pattern for collaborative software work. For any serious platform, version control would normally support feature branches, review, merge discipline, and release tagging.
So a credible explanation of how HCS 411GITS software built would include:
- A stable main branch
- Feature branches for new work
- Code review before merging
- Release tags or version checkpoints
- Rollback capability when problems appear
While this does not confirm specific tools, it reflects widely adopted industry practices relevant to How HCS 411GITS Software Built.
4. Testing and verification
Martin Fowler describes Continuous Integration as integrating code frequently and verifying it through automated builds and tests so integration problems are found earlier. That principle matters even more for software that appears to involve workflows, updates, or multiple connected components.
A realistic testing approach would include:
- Unit testing for isolated functions
- Integration testing for connected components
- System testing for end-to-end behavior
- Regression testing after changes
- Performance testing under load
- Security testing and review
This is an inference from standard engineering practices, but it strongly supports understanding How HCS 411GITS Software Built in a reliable and scalable way.
5. Deployment, operations, and maintenance
The forum thread explicitly mentions deployment to local servers, cloud platforms, or containers as general software-development possibilities, but that thread is still generic advice rather than verified HCS 411GITS documentation. More broadly, any platform discussed as updated, maintained, or enterprise-relevant would normally need staging, production release controls, monitoring, and post-release support.
A careful explanation of How HCS 411GITS Software Built includes a lifecycle of:
- Build
- Test
- Deploy
- Monitor
- Patch
- Improve
This continuous cycle reflects how modern software systems are maintained over time. Understanding this lifecycle is essential to fully grasp How HCS 411GITS Software Built and how such platforms evolve after initial release.
Key Features HCS 411GITS Likely Includes
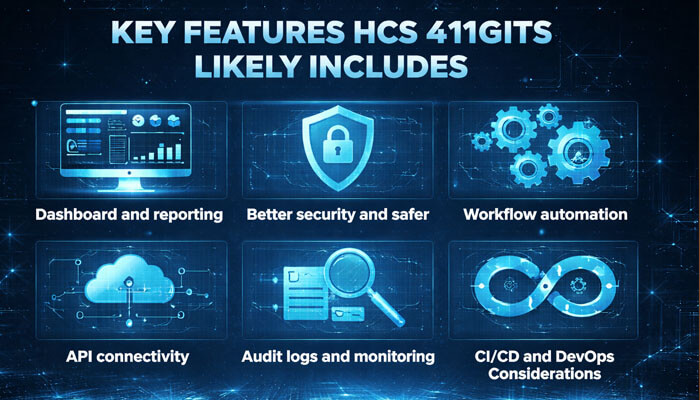
| Likely feature | User benefit |
|---|---|
| Dashboard and reporting | Faster visibility into operations |
| User access controls | Better security and safer workflows |
| Workflow automation | Reduces manual effort |
| API connectivity | Easier integration with other systems |
| Audit logs | Better accountability and tracking |
| Monitoring and alerts | Faster issue detection |
A good article should also explain what the software probably does, while still signalling uncertainty where needed. This balanced approach is essential when analyzing How HCS 411GITS Software Built without relying on unverified claims.
Dashboard and reporting
Multiple sources imply a system with visibility, control, or operations. That makes dashboard-style interfaces and reporting highly plausible. ScoopMeadow explicitly mentions operator-centric dashboards, while StartupBooted describes the software more broadly as structured and workflow-oriented. These patterns align with how HCS 411GITS Software Built would support real-time insights and decision-making.
User access controls
Any software that supports multiple workflows or roles usually needs permission-based access. NIST and OWASP both emphasize secure design and verification practices that align with role separation, least privilege, and controlled access. This is a strong indicator when evaluating How HCS 411GITS Software Built in terms of security and user management.
Workflow automation
BusinessAndPower discusses updates, integrations, and migration-style concerns that fit a platform with rule-based processes and change-sensitive operations. That makes workflow automation a reasonable inference, though not a confirmed product specification. It also reflects common patterns in How HCS 411GITS Software Built for efficiency and scalability.
API connectivity
BusinessAndPower’s discussion of webhook and API-related changes makes integration a particularly plausible part of the software’s design, though again that source is secondary.
Integration capabilities are a key aspect of How HCS 411GITS Software Built, especially for systems interacting with multiple external platforms.
Audit logs and monitoring
If the software handles structured operations or enterprise-like updates, auditability and monitoring are practical necessities. OWASP secure-development guidance also supports the broader importance of verification and operational security. These elements are central to understanding How HCS 411GITS Software Built in secure and traceable environments.
CI/CD and DevOps Considerations
A trustworthy version of this article should mention DevOps, but carefully. The Mepis thread mentions CI/CD as a general development practice, and Fowler’s explanation of Continuous Integration supports the idea that modern teams reduce delivery risk through frequent integration and automated verification.
For software like HCS 411GITS, a likely DevOps workflow would involve:
- Code committed to version control
- Automated builds
- Tests run on change
- Staging validation
- Controlled release to production
- Post-release monitoring
- Rollback when needed
This is not a confirmed internal pipeline. It is the most credible description of How HCS 411GITS Software Built and maintained using modern engineering practices.
Scalability and Performance
This is another section where the article should stay grounded. ScoopMeadow makes strong claims about real-time processing, scale, and hybrid edge-cloud architecture, but because those claims come from a secondary site, they should be treated as unverified descriptions rather than hard fact. Still, if HCS 411GITS really is intended for complex workflows or real-time environments, the software would likely need scalability practices such as database tuning, caching, modular service separation, and ongoing monitoring.
That makes it reasonable to discuss performance topics like:
- Query optimization
- Caching
- Log analysis
- Load distribution
- Service isolation
- Performance monitoring
Common Challenges in Building HCS 411GITS-Type Software
Understanding the challenges helps provide deeper insight into How HCS 411GITS Software Built in real-world scenarios, especially for complex and workflow-driven systems.
| Challenge | Why it happens | Likely solution |
|---|---|---|
| Integration complexity | Multiple systems must connect | API standardization and testing |
| Performance bottlenecks | Increased users and data | Caching, indexing, monitoring |
| Workflow rigidity | Hard-coded logic | Flexible workflow design |
| Security gaps | Late implementation | Secure-by-design approach |
| Maintenance overhead | System grows over time | Documentation and structured updates |
These challenges are common across enterprise-grade platforms and reflect practical considerations in How HCS 411GITS Software Built for scalability and reliability.
User Roles and Permissions
A workflow-oriented platform usually separates access by role. That keeps sensitive actions limited to the right users and reduces mistakes. NIST and OWASP both support designing secure systems with appropriate controls built in from the start. This aligns closely with best practices in How HCS 411GITS Software Built for secure and controlled environments.
Typical role patterns could include:
| Role | Likely access level | Main responsibility |
|---|---|---|
| Admin | Full | System control, settings, user management |
| Manager | High | Oversight, approvals, reporting |
| Operator | Medium | Daily workflow execution |
| Analyst | Limited | Data analysis and reporting |
| Viewer | Read-only | Monitoring and visibility |
These are example roles, not documented HCS 411GITS role names, but they reflect realistic structures in How HCS 411GITS Software Built for managing user access and responsibilities.
What Cannot Be Confirmed Publicly
This is the most important trust-building section in the article. Recognizing limitations is essential when analyzing How HCS 411GITS Software Built based on available information.
At this point, the available public sources do not clearly verify:
- The official vendor or publisher of HCS 411GITS
- The exact programming languages used internally
- The exact database engine
- The exact hosting model
- Whether all public pages refer to the same product in the same way
- Whether the smart-traffic framing and the enterprise-workflow framing are describing one system or overlapping interpretations
That uncertainty is real. The sources you provided do not line up neatly enough to support a fully verified technical profile. This is why discussions about How HCS 411GITS Software Built must rely on cautious interpretation rather than definitive claims.
Why Understanding How HCS 411GITS Software Built Matters
Understanding How HCS 411GITS Software Built helps users and businesses make better technical decisions. When software is built using structured architecture, secure development practices, and scalable systems, it becomes more reliable, easier to maintain, and safer to use.
It also helps avoid false assumptions. Since public information about HCS 411GITS is limited and sometimes inconsistent, knowing how such systems are typically built allows readers to evaluate risks, performance expectations, and long-term usability more realistically. This makes analyzing How HCS 411GITS Software Built especially important for accurate understanding.
A clear perspective on How HCS 411GITS Software Built also supports better planning, system integration, and informed decision-making when working with similar software platforms.
Pros and Cons of HCS 411GITS
Evaluating advantages and limitations is another key part of understanding How HCS 411GITS Software Built and how it performs in real-world scenarios.
| Pros | Cons |
|---|---|
| Structured workflow-based design | No official documentation available |
| Modular and scalable architecture | Conflicting descriptions across sources |
| Supports integration and automation | Technology stack not confirmed |
| Strong security practices implied | Relies partly on secondary sources |
These points highlight both the strengths and uncertainties surrounding the system. Recognizing them is essential when interpreting How HCS 411GITS Software Built in the absence of fully verified technical documentation.
How HCS 411GITS Software Built FAQs
1. Can beginners understand how HCS 411GITS software built?
Yes, beginners can understand how HCS 411GITS software built by focusing on basic concepts like planning, architecture, and testing rather than technical details.
2. How HCS 411GITS software built affects system performance?
How HCS 411GITS software built directly impacts performance through scalability design, database optimization, and efficient workflow handling.
3. Is how HCS 411GITS software built similar to modern enterprise software?
Yes, how HCS 411GITS software built appears to follow patterns similar to modern enterprise platforms using modular design and structured workflows.
4. Why is it hard to verify how HCS 411GITS software built?
It is hard to verify how HCS 411GITS software built because most available information comes from secondary sources, not official documentation.
5. Does how HCS 411GITS software built impact security?
Yes, how HCS 411GITS software built affects security through authentication systems, access control, and secure development practices.